- Main
- Computers - Databases
- Machine Learning and Security:...

Machine Learning and Security: Protecting Systems with Data and Algorithms
Clarence Chio, David FreemanHow much do you like this book?
What’s the quality of the file?
Download the book for quality assessment
What’s the quality of the downloaded files?
Can machine learning techniques solve our computer security problems and finally put an end to the cat-and-mouse game between attackers and defenders? Or is this hope merely hype? Now you can dive into the science and answer this question for yourself. With this practical guide, you'll explore ways to apply machine learning to security issues such as intrusion detection, malware classification, and network analysis.
Machine learning and security specialists Clarence Chio and David Freeman provide a framework for discussing the marriage of these two fields, as well as a toolkit of machine-learning algorithms that you can apply to an array of security problems. This book is ideal for security engineers and data scientists alike.
Learn how machine learning has contributed to the success of modern spam filters
Quickly detect anomalies, including breaches, fraud, and impending system failure
Conduct malware analysis by extracting useful information from computer binaries
Uncover attackers within the network by finding patterns inside datasets
Examine how attackers exploit consumer-facing websites and app functionality
Translate your machine learning algorithms from the lab to production
Understand the threat attackers pose to machine learning solutions
Machine learning and security specialists Clarence Chio and David Freeman provide a framework for discussing the marriage of these two fields, as well as a toolkit of machine-learning algorithms that you can apply to an array of security problems. This book is ideal for security engineers and data scientists alike.
Learn how machine learning has contributed to the success of modern spam filters
Quickly detect anomalies, including breaches, fraud, and impending system failure
Conduct malware analysis by extracting useful information from computer binaries
Uncover attackers within the network by finding patterns inside datasets
Examine how attackers exploit consumer-facing websites and app functionality
Translate your machine learning algorithms from the lab to production
Understand the threat attackers pose to machine learning solutions
Categories:
Year:
2018
Publisher:
O’Reilly Media
Language:
english
Pages:
386
ISBN 10:
1491979909
ISBN 13:
9781491979907
File:
PDF, 4.22 MB
Your tags:
IPFS:
CID , CID Blake2b
english, 2018
The file will be sent to your email address. It may take up to 1-5 minutes before you receive it.
The file will be sent to you via the Telegram messenger. It may take up to 1-5 minutes before you receive it.
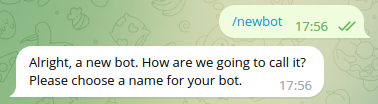
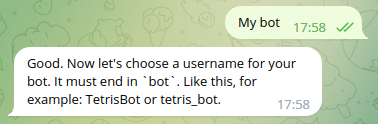
Note: Make sure you have linked your account to Z-Library Telegram bot.
The file will be sent to your Kindle account. It may take up to 1–5 minutes before you receive it.
Please note: you need to verify every book you want to send to your Kindle. Check your mailbox for the verification email from Amazon Kindle.
Conversion to is in progress
Conversion to is failed
Premium benefits
- Send to eReaders
- Increased download limit
 File converter
File converter More search results
More search results More benefits
More benefits
Most frequently terms
Related Booklists


























































































 Amazon
Amazon  Barnes & Noble
Barnes & Noble  Bookshop.org
Bookshop.org 















![Aurelien Geron [Géron, Aurélien] — Hands-On Machine Learning with Scikit-Learn, Keras, and TensorFlow: Concepts, Tools, and Techniques to Build Intelligent Systems](https://s3proxy.cdn-zlib.se/covers200/collections/genesis/3326682644fad9b9f7839b29b9023cbe1e9175df9a44ed0617dd4535ce2e1f14.jpg)